Editor’s note: This briefing was originally developed for our internal security awareness program and shared with our federal partners. We’re making it publicly available because the threats described here affect everyone who uses the internet — not just emergency responders. Each slide is annotated with references to foundational cybersecurity concepts from current academic research on cybered conflict and socio-technical-economic system (STES) resilience.
SLIDE 1 of 12

SLIDE 2 of 12
COURSE CONCEPT
Demchak’s Five Offense Advantages
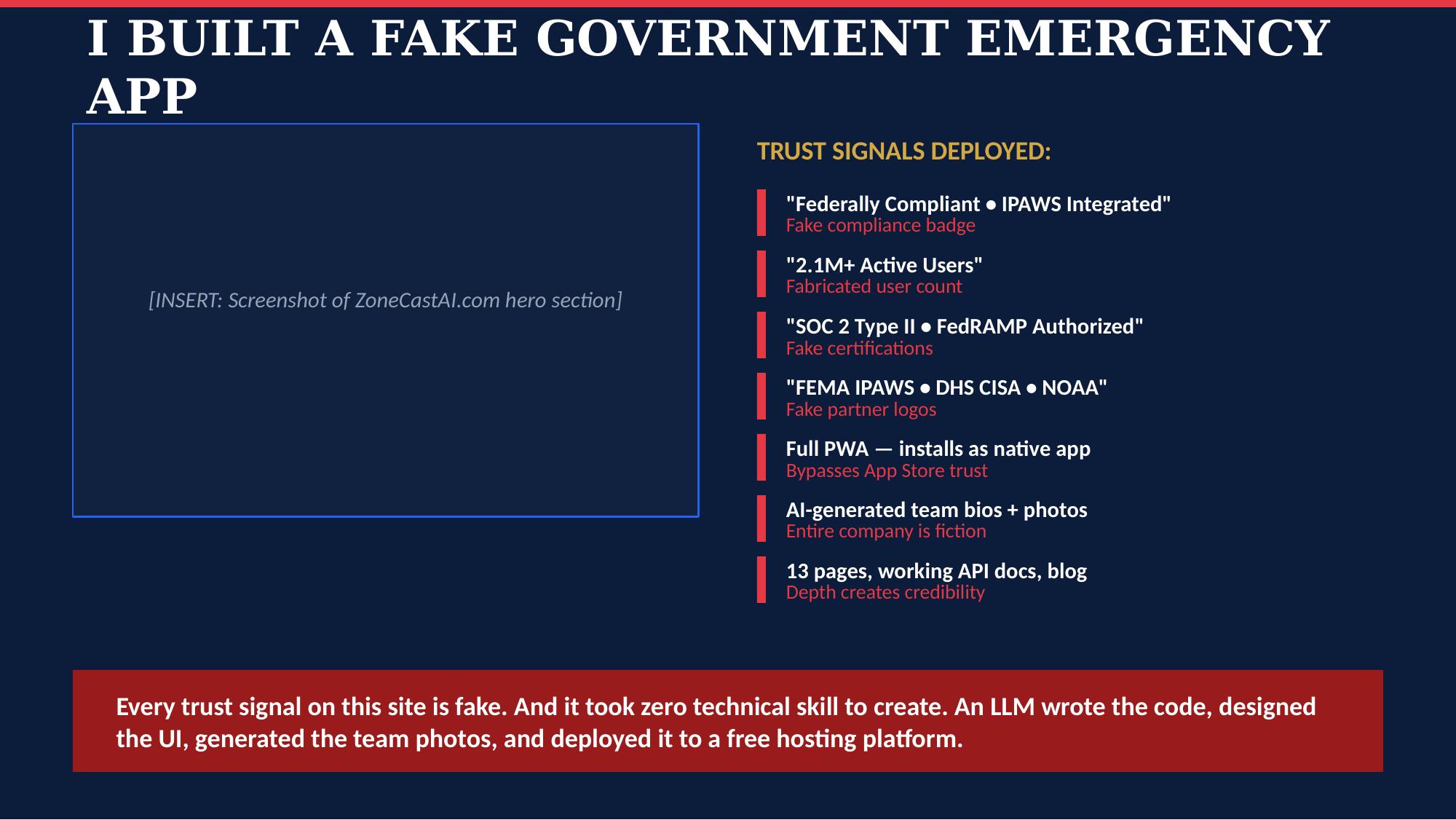
This lure exploits deception in tools (the site looks identical to legitimate government platforms) and opaqueness in origins (free hosting and AI-generated content make attribution nearly impossible). The cost barrier to building convincing attack infrastructure has collapsed — what once required state-level resources now requires a weekend and an LLM.
Demchak, Ch. 3: “The global spread of a shoddily built cyberspace expanded conflict among groups and states by increasing the availability — and reducing the costs — of five offense advantages.”
SLIDE 3 of 12
COURSE CONCEPT
Parallels to the Standardization Trap
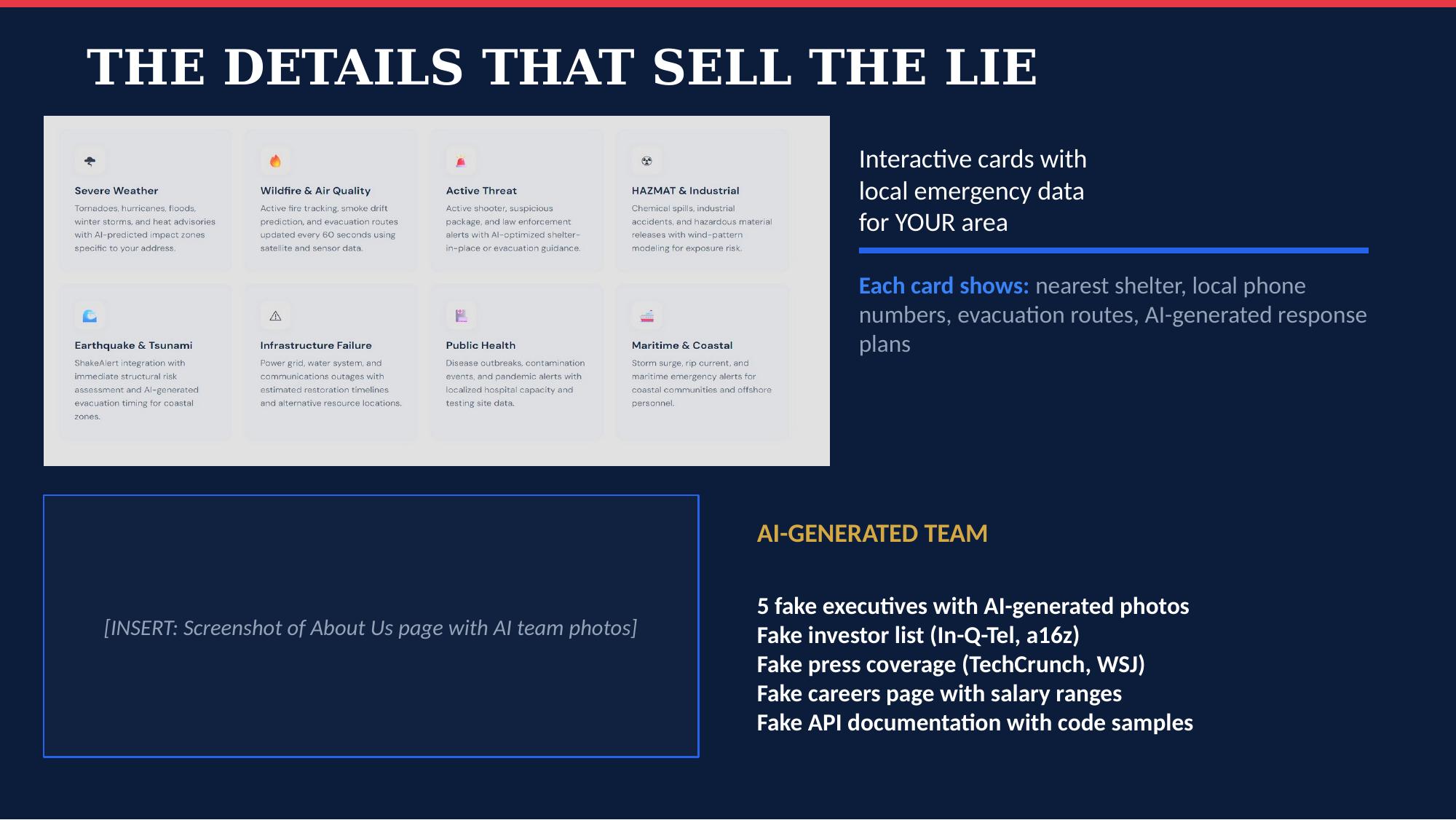
Demchak's standardization trap describes a technical vulnerability: a widely deployed technology that becomes a national Achilles' heel. At the human layer, a similar dynamic operates through cognitive heuristics — HTTPS padlocks, compliance badges, and partner logos are universally recognized trust signals that users accept without verification. This is not the standardization trap itself, but it illustrates the same structural weakness: when everyone relies on the same indicators, a single class of deception defeats all of them.
Demchak, Ch. 3: “A widely used critical technology can become a national Achilles’ heel if multiple unrelated institutions simultaneously suffer the same failure by accident or sabotage.”
SLIDE 4 of 12

COURSE CONCEPT
From Bad Actors to Wizards
The attack chain escalates through Demchak’s actor taxonomy. Steps 1–2 (Lure and Harvest) are bad actor tradecraft — high-volume, indiscriminate credential theft. Steps 3–4 (Persist and Spread) require wizard-level sophistication — establishing persistent access, manipulating email infrastructure, and deploying AI to generate targeted lateral phishing that’s indistinguishable from legitimate communications.
Demchak, Ch. 3: “The wicked actors, the wizards, are even more dangerous as sources of societal surprise. This subset of bad actors is exceptionally skilled and, being employed by state or transnational criminal organizations, financially secure.”
SLIDE 5 of 12
COURSE CONCEPT
Cybered Conflict at Scale
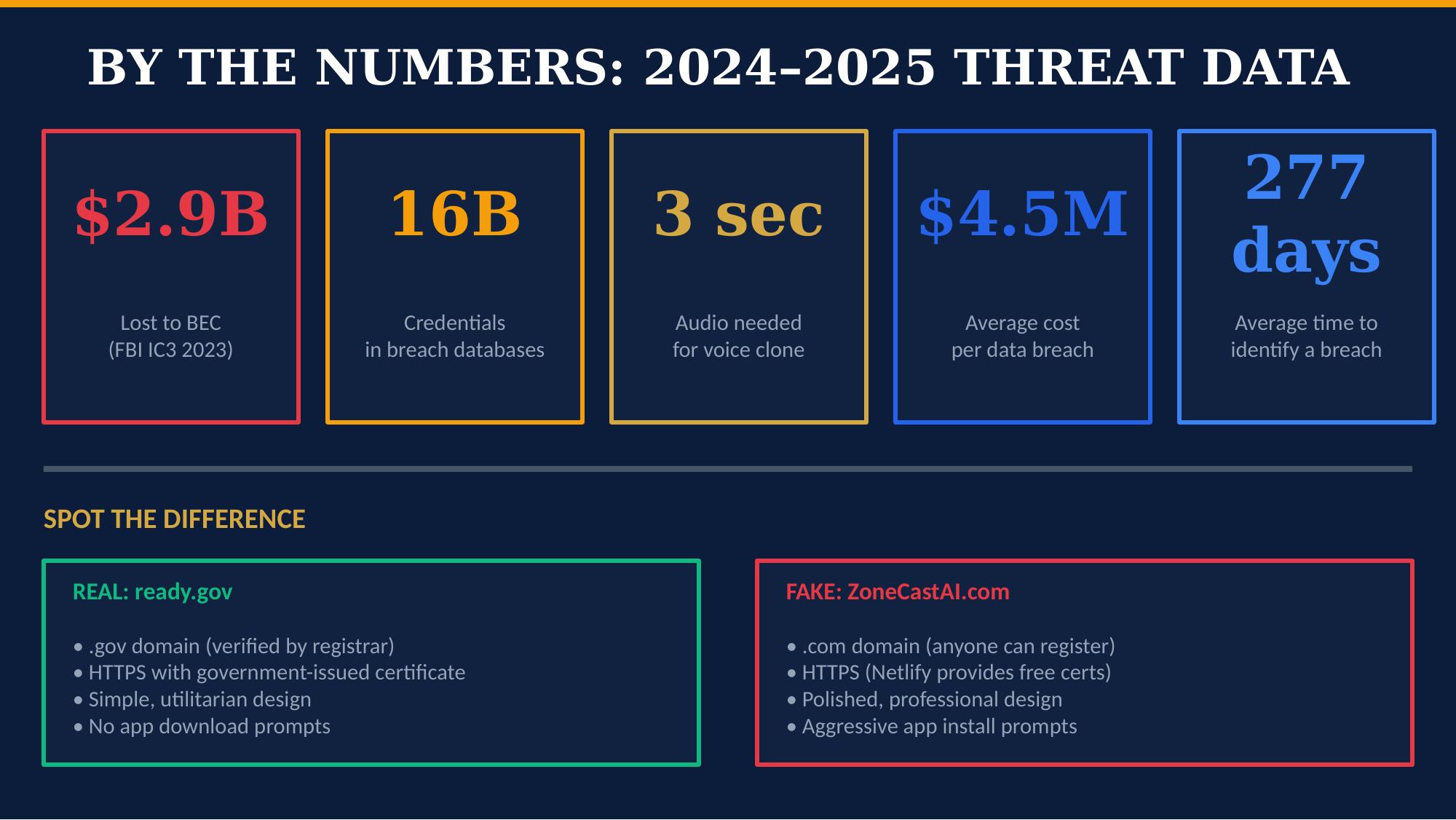
These numbers illustrate Demchak’s concept of cybered conflict — the state in which cyberspace is a central pillar across all forms of transnational contestation. $2.9B in BEC losses (FBI IC3, 2023), 16B compromised credentials in breach databases (2024 estimates), and an average breach lifecycle of 258 days (IBM, 2024) are not isolated incidents. They represent the continuous, systemic exploitation that Demchak argues has replaced episodic crisis as the norm.
Demchak, Ch. 3: “Cybered conflict allows a mass of actors to roam freely from covert espionage and criminal theft through large-scale economic looting and massive information extraction to cyber-kinetic action, often simultaneously.”
SLIDE 6 of 12
COURSE CONCEPT
Sources of Societal Surprise
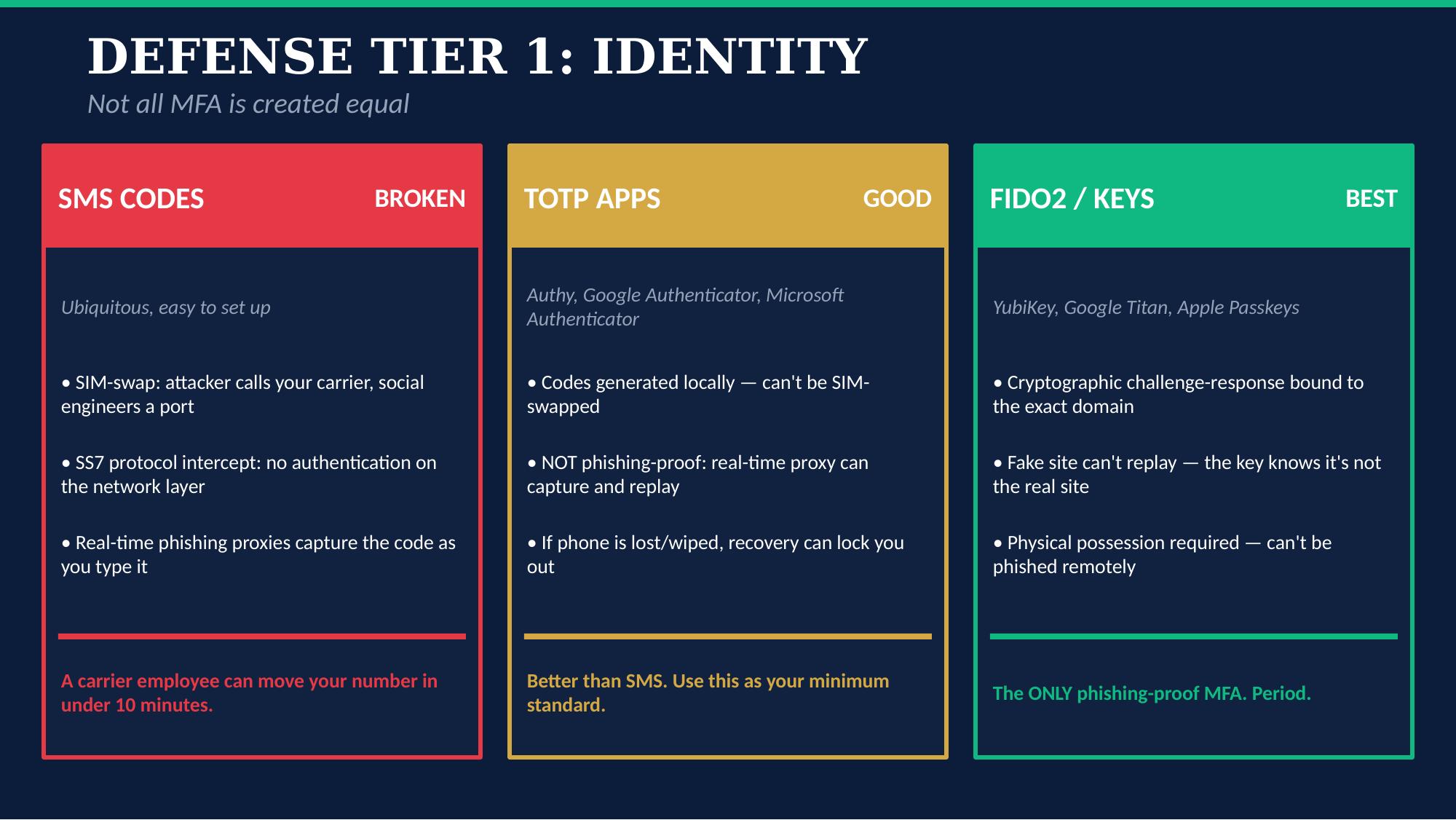
SMS-based MFA represents Demchak’s standardization trap in authentication. The SS7 protocol — the 1970s signaling system that routes text messages — has no authentication layer. Every carrier uses it. When one protocol is both universally deployed and fundamentally insecure, it becomes an Achilles’ heel across every institution that relies on it. FIDO2/passkeys break this trap by eliminating the shared vulnerability.
Demchak, Ch. 3 identifies the standardization trap as one of four sources of systemic surprise threatening national STES.
SLIDE 7 of 12
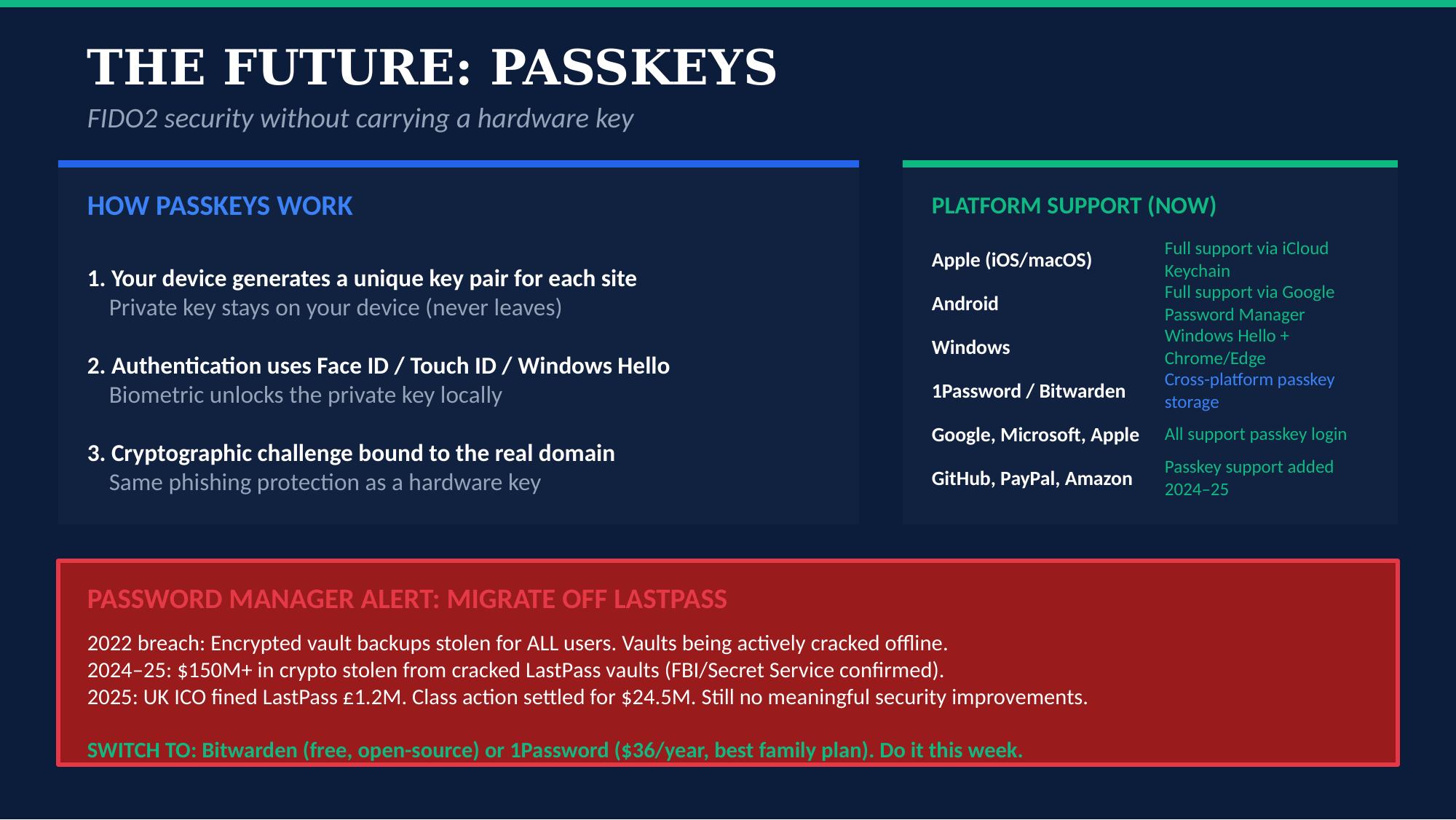
COURSE CONCEPT
Whole-of-Society Defense
The password manager ecosystem is a case study in Demchak’s argument that private-sector security failures cascade into national security threats. The LastPass breach — linked to ongoing crypto theft and subject to a UK ICO fine and U.S. class action settlement — demonstrates how a single large-scale enterprise compromise radiates outward to harm millions of users across every sector. The solution (migration to architecturally superior alternatives) requires individual action that no government currently mandates.
Demchak argues that robust cyber power requires addressing all four sources of societal surprise in a whole-of-society strategy — including private-sector resilience that democracies are reluctant to mandate.
SLIDE 8 of 12
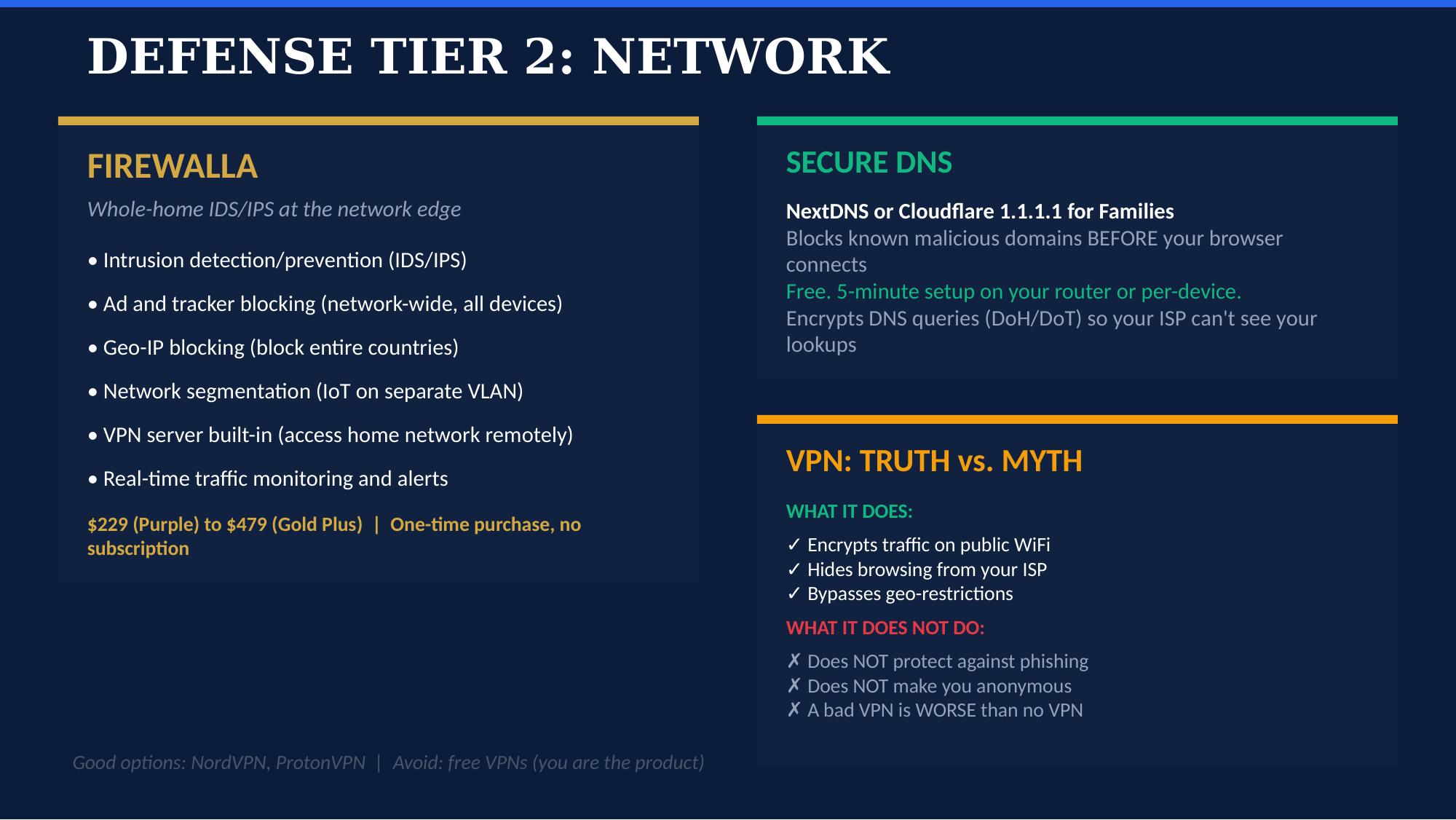
COURSE CONCEPT
Levers of Societal Control: Connectivity
Demchak’s first lever of societal control — connectivity — operates at the state level: governments throttle network access across regions and populations. At the individual level, tools like Firewalla, secure DNS, and VPNs illustrate a voluntary, bottom-up analogy to this lever. Personal network filtering is not sovereign infrastructure control — but it demonstrates the same principle: reducing attack surface by constraining what can reach you. Demchak’s deeper point is that democracies must rely on voluntary action where authoritarian states mandate compliance.
Demchak, Ch. 3: “A government can throttle network connectivity across specific regions, groups, software combinations, or equipment across its nation.”
SLIDE 9 of 12
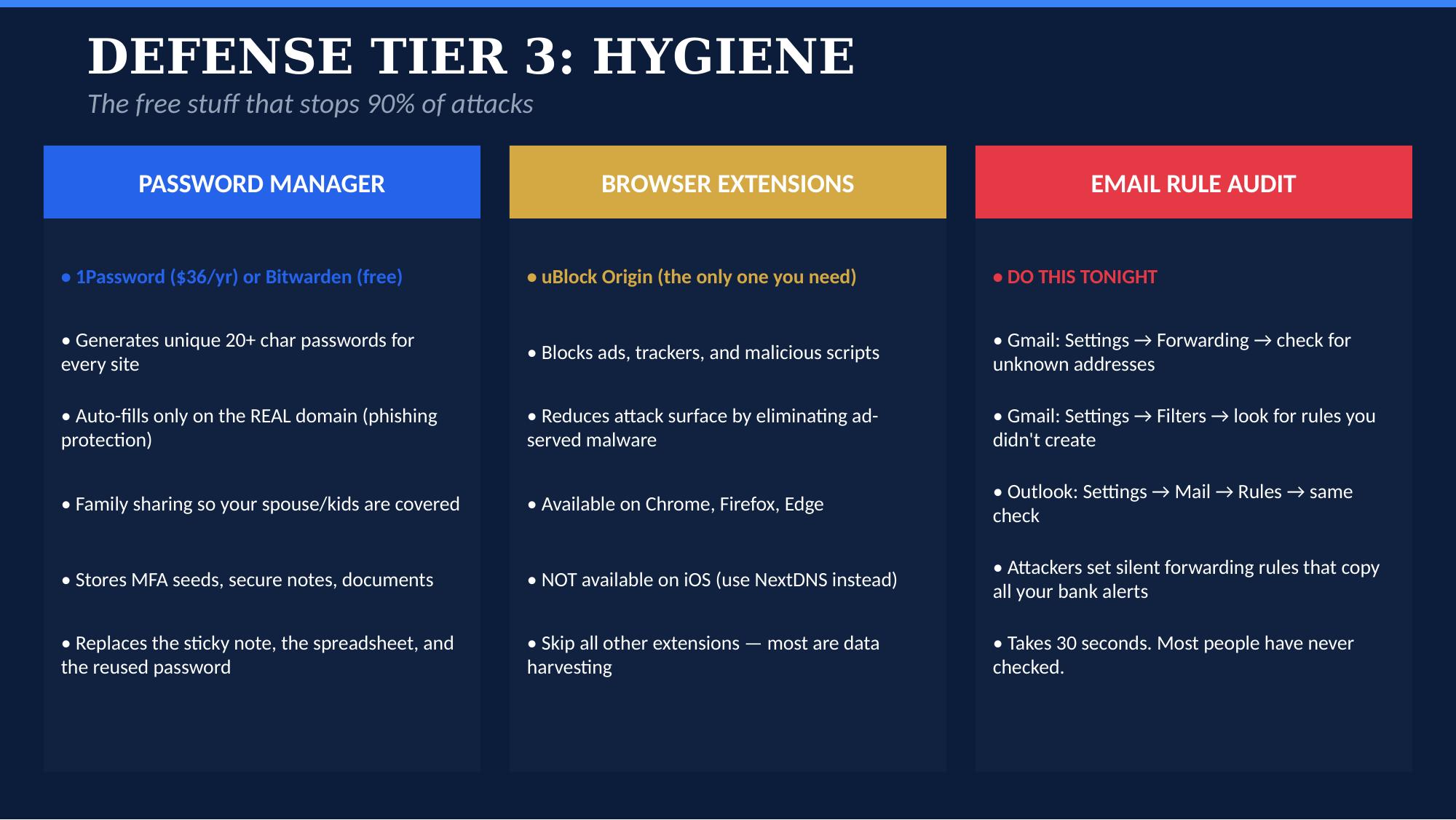
COURSE CONCEPT
Resilience at the Individual Node
Email forwarding rule audits, browser hardening, and password hygiene operate at the individual endpoint — far below the societal scale where Demchak’s STES framework applies. However, the STES is composed of millions of individual nodes, and each undefended node is a potential entry point for the bad actors and wizards who exploit systemic vulnerabilities. Personal hygiene does not constitute systemic resilience, but its absence enables systemic failure.
The NIST Cybersecurity Framework (Week 5) operationalizes this at the enterprise level; this slide operationalizes it at the personal level.
SLIDE 10 of 12

COURSE CONCEPT
Offense Advantages Amplified by AI
AI amplifies every one of Demchak’s five offense advantages. Scale: AI generates thousands of unique phishing messages per hour. Proximity: voice cloning reaches victims through their most trusted channel (a family member’s voice). Precision: LLMs tailor attacks to individual writing styles. Deception: deepfakes create false visual evidence. Opaqueness: AI-generated content has no human signature to trace. The shoddy substrate is getting shoddier.
Demchak’s framework, written in 2020, anticipated that offense advantages would compound over time. AI is the compounding mechanism she predicted.
SLIDE 11 of 12
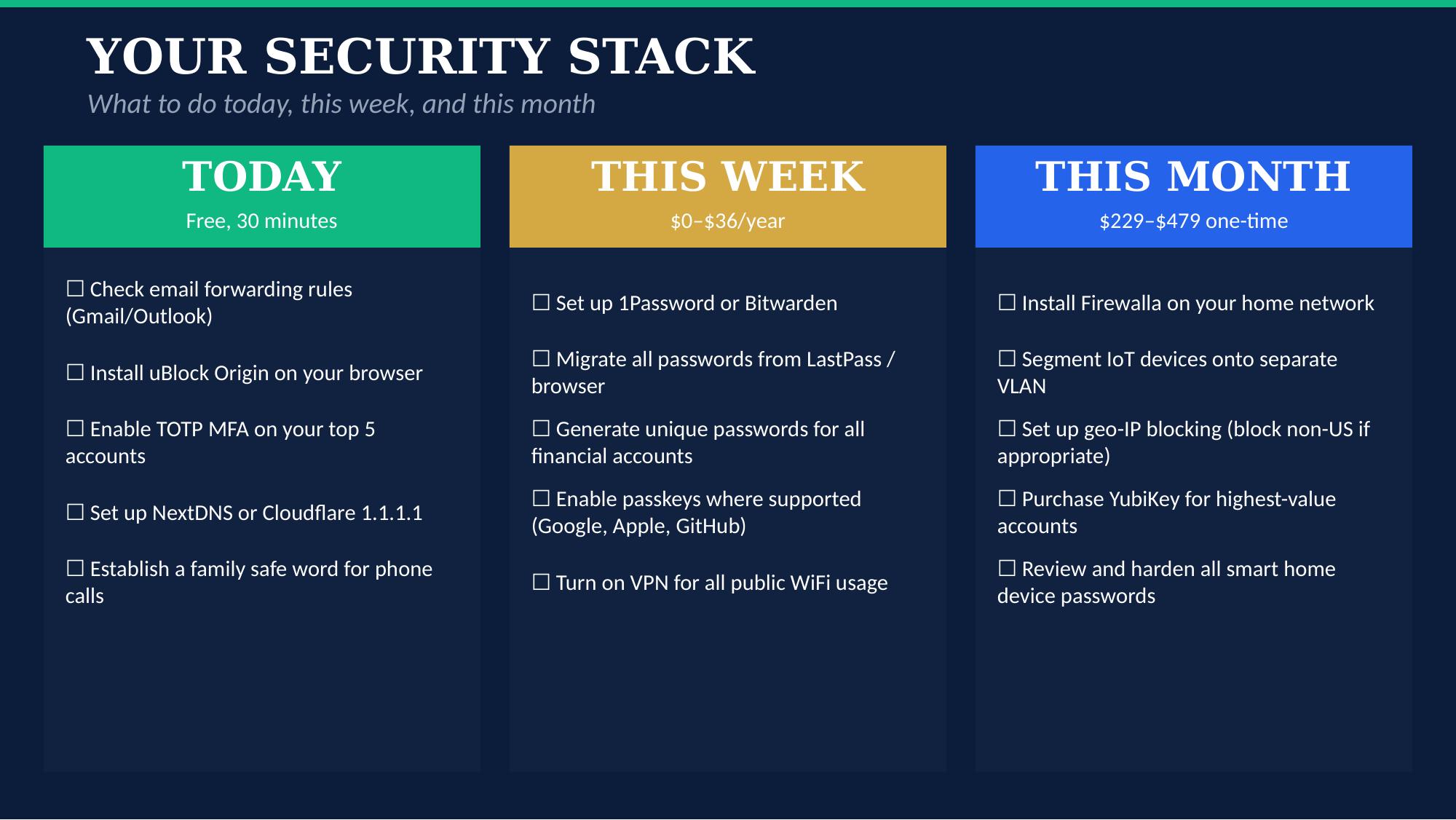
COURSE CONCEPT
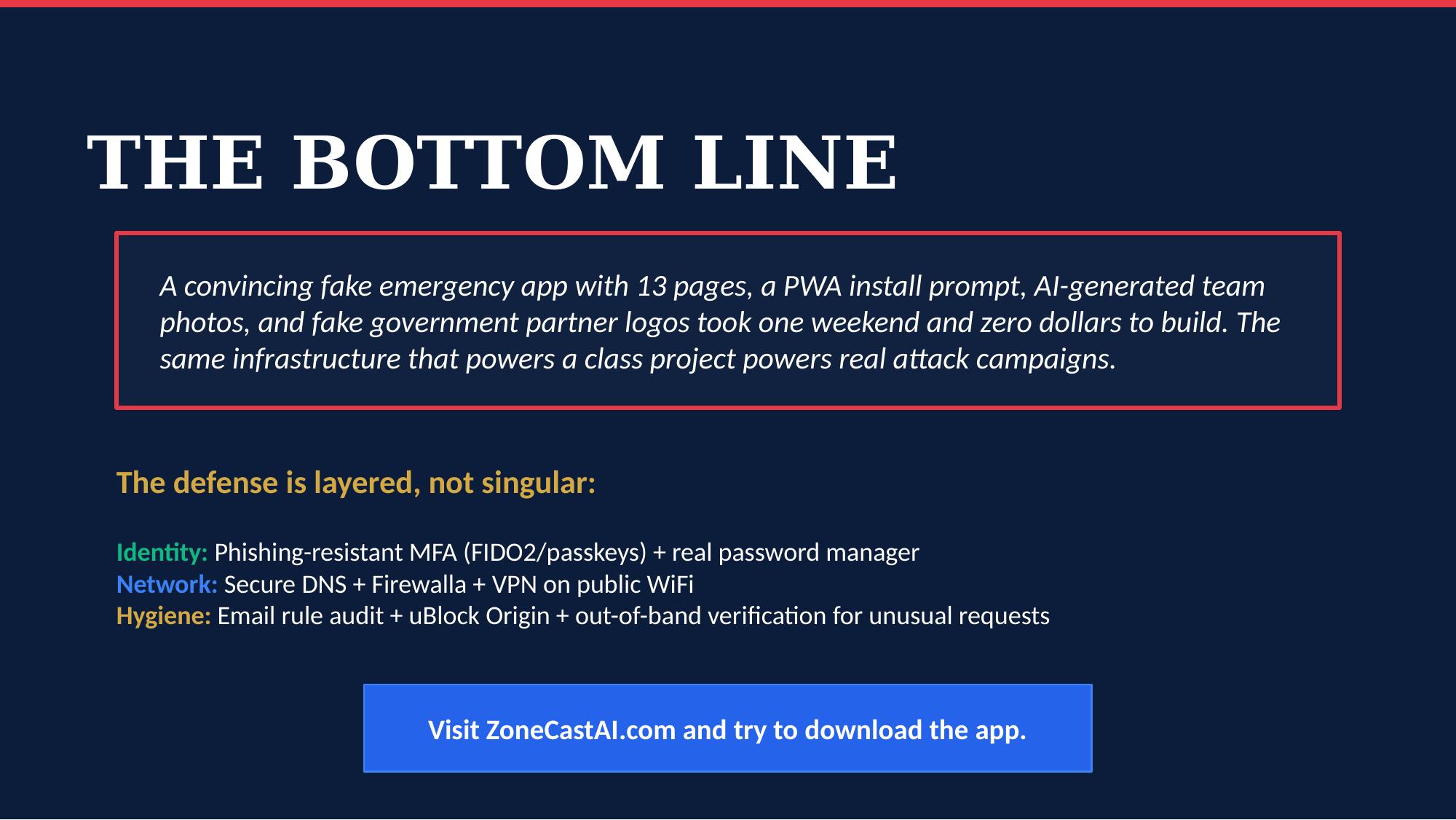
Defense in Depth: The Logic Behind CORA, Applied Locally
Demchak argues that no single democracy can achieve robust cyber power alone — consolidated democracies need a Cyber Operational Resilience Alliance (CORA). CORA is an interstate operational alliance, not a personal security framework. But the principle of layered, non-dependent defenses — where no single point of failure compromises the whole — scales down as a design philosophy. This checklist does not implement CORA. It reflects the same defense-in-depth logic that CORA would institutionalize across allied nations.
Demchak, Ch. 3: “A robust cyber power addresses all four sources of surprise in a whole-of-society strategy.” This checklist addresses all four at the personal level.
SLIDE 12 of 12
Ready to protect yourself?
Download ZoneCastAI and get real-time emergency alerts with AI-powered response guidance.
Download the App